Ransomware and cyberattacks have seen a significant increase in frequency and severity in the last few years, supercharged in part by the workforce moving to a largely remote model during the pandemic. As businesses depend more on technology infrastructure and cloud operations, the vulnerabilities of these systems are being exploited by cybercriminals. While cyberattacks reported in the media mainly focus on large corporations, the reality is small businesses, with fewer resources and less technical expertise, are often seen as easy targets for cyberattacks.
AdvisorSmith conducted a survey of 1,122 small business owners and managers to understand their experiences with cyberattacks and how their businesses are preparing for cyber threats.
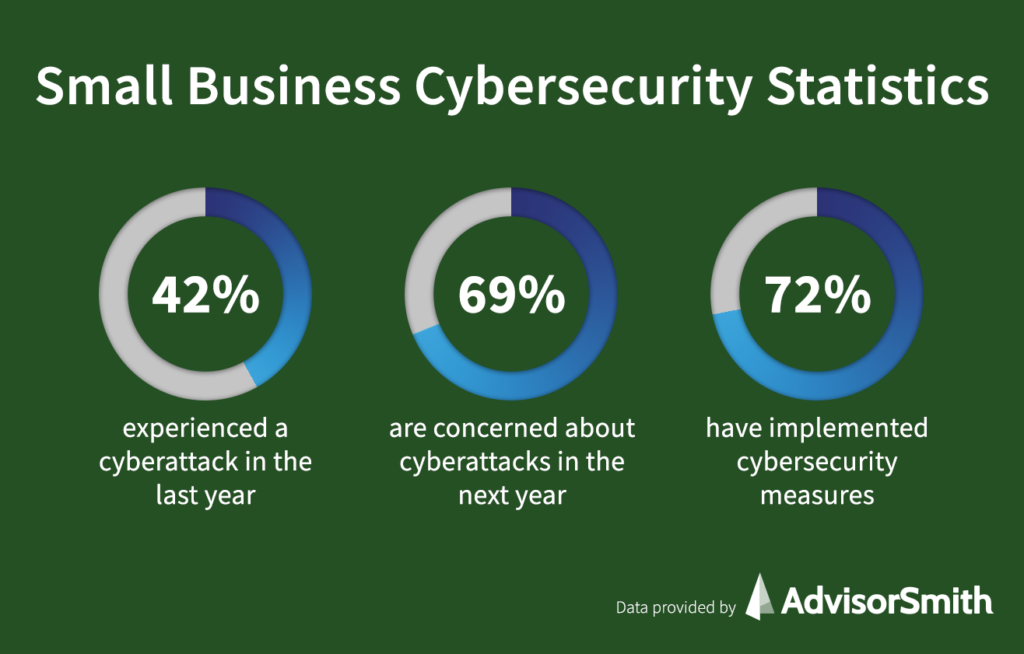
42% of small businesses experienced a cyberattack in the last year
Nearly half (41.8%) of all small businesses were the victim of a cyberattack in the last 12 months, according to our survey. The following is a breakdown of the types of cyberattacks that these small businesses suffered:
- 23.7%: Phishing attack. A phishing attack occurs when a cybercriminal poses as a trusted authority in order to gain personal information like passwords or credit card numbers. Businesses are increasingly seeing more phishing attempts, particularly spear phishing attacks, which target specific employees and generally see a higher success rate.
- 18.6%: Data breach. A data breach occurs when your business’s private or confidential data is accessed by an unauthorized party.
- 16.5%: Malware attack. A malware attack is executed by malicious software.
- 14.8%: Denial of service (DoS) attack. A denial of service attack is meant to take down a victim’s network or system through a flood of malicious traffic.
- 11.3%: Ransomware attack. A ransomware attack occurs when a cyberciminal gains access to your business device and locks down the system or blocks certain resources until your business pays a ransom. These attacks are becoming increasingly common, particularly as ransomware-as-a-service (RaaS) has emerged, allowing even those without technical expertise to execute ransomware attacks by paying for the service.
- 15.0%: Other cyberattack.
69% of small businesses are concerned about being the victim of a cyberattack
Our survey showed that overall, 69.2% of small business owners were concerned about being the victim of a cyberattack in the next 12 months, with 24.9% saying they were “very concerned,” 44.3% saying they were “somewhat concerned,” and 30.8% saying they were “not concerned at all.”
Younger business owners 1.8x more likely to be concerned about cyber threats
Interestingly, an active concern about cyber threats skewed younger, with 31.2% of those business owners aged 18-29 saying they were “very concerned,” compared to only 17.1% of those aged over 60, 23.3% of those between ages 45-60, and 24.3% of those between ages 30-44. The same trend was seen for those who said they were “not concerned at all,” with 34.2% of those 60 and older not having any concerns about cyber threats, compared to only 23% of those aged between 18-29.
| Age | Very concerned | Somewhat concerned | Not concerned at all |
|---|---|---|---|
| 18-29 | 31.15% | 45.90% | 22.95% |
| 30-44 | 24.28% | 41.87% | 33.85% |
| 45-60 | 23.30% | 43.20% | 33.50% |
| 61+ | 17.09% | 48.73% | 34.18% |
This trend may prove beneficial for cybercriminals, as oftentimes, it is the older generation that is actually targeted more heavily for fraud and identity theft because they may be less technically savvy than younger individuals.
72% of small businesses have implemented cybersecurity precautions
A majority (72.0%) of small business owners and managers have prepared in some way for the threat of a cyberattack. While this seems like a promising step, there is still 28% of respondents that have not implemented any form of cybersecurity protocols. Even a few basic cybersecurity measures can make a big difference in helping your business ward off cyberattacks and data breaches.
The following is a breakdown of the types of cybersecurity preparations small businesses have taken:
- 21.3%: We have implemented a strong password policy.
- 20.4%: We have implemented multi-factor authentication.
- 16.6%: We have implemented data encryption.
- 16.4%: We have purchased cybersecurity software.
- 15.9%: We regularly train our employees on cybersecurity.
- 9.4%: We have hired a cybersecurity consultant.
1 in 2 small businesses have or plan on purchasing cyber insurance
While there is no silver bullet to protecting your business from cyber threats, and no business can ever be 100% fully protected, small businesses are increasingly purchasing the financial protection of cyber insurance, which can cover your business against liability and property losses caused by cyberattacks.
In our survey, 23% of respondents indicated that they planned on purchasing cyber insurance in the next 12 months, 12.8% already had cyber insurance, and 17.9% had cyber insurance and were planning on increasing their coverage in the next 12 months. On the flip side, 46.3% of respondents did not have cyber insurance and had no plans of purchasing the coverage.
Younger business owners 3x more likely to purchase cyber insurance
While overall, roughly half of small business owners had or were planning on purchasing cyber insurance in the next 12 months, the distribution skewed very much toward younger business owners, who were far more likely to secure cyber coverage.
Seventy-five percent (75.7%) of those business owners between the ages of 18-29 indicated they already had cyber insurance or were looking to purchase, while only 28.5% of those over the age of 60 said the same. Forty-three percent (43.2%) of those between ages 45-60 and 52.3% of those between ages 30-44 had or were planning on purchasing cyber insurance.
| Age | Plan on purchasing cyber insurance | Have cyber insurance | Have cyber insurance, plan to increase coverage | No cyber insurance, no plans to purchase |
|---|---|---|---|---|
| 18-29 | 31.80% | 15.08% | 28.85% | 24.26% |
| 30-44 | 23.61% | 10.47% | 18.26% | 47.66% |
| 45-60 | 20.87% | 12.62% | 9.71% | 56.80% |
| 61+ | 6.96% | 15.19% | 6.33% | 71.52% |
Protecting Your Small Business Against Cyberattacks
For small businesses, just one cyberattack could mean losses and damages that are irrecoverable. To combat the threat of a cyberattack, consider taking these simple actions to beef up your cybersecurity:
- Practice good login/password techniques. It’s not surprising that many successful cyberattacks stem from exploiting common or easily-guessed passwords. A little bit of password rigor can go a long way. Make sure you’re not using the same login and password across multiple accounts, create strong passwords (and require your employees to do the same), and consider using a password manager, like 1Password, which can automatically create strong passwords for you. For even higher levels of protection, use two-factor authentication, which forces you to confirm your identity with extra information, like a phone number or unique security code.
- Train your employees. You know what they say about the weakest link—all it takes is one employee to fall for a scam or get hacked for your entire business to be vulnerable. Make sure you are educating your employees on basic cybersecurity, like recognizing common phishing attacks, avoiding opening attachments or clicking on links from unverified sources, and implementing strong passwords.
- Keep your systems up to date. Many of the most famous cyberattacks took advantage of out-of-date software and known vulnerabilities. Make sure that your computers and network systems are always updated to the latest versions. Many of these updates are specifically to plug security holes, so it’s important to ensure you and your employees take the time to update all devices.
- Backup your data. If your data is ever held hostage, deleted, or lost, you’ll be thankful you had a backup in place. While you can subscribe to cloud backup services like Backblaze, it’s also wise to keep a physical backup of your data.
- Use security software. Many operating systems already come built-in with security and antivirus software, so you’re more than likely already decently protected from known viruses and attacks (just make sure your software is updated and activated). However, if you are on an older operating system, you may want to consider purchasing an off-the-shelf security product, e.g. Norton 360.
- Restrict access to sensitive data. By limiting the people at your company who have access to certain files, you’ll be lowering the risk of those files being hacked or that data being breached. Make sure you’re implementing varying levels of security access, with the most confidential data being shared with only those who absolutely need access.
- Invest in cyber insurance. Even with security measures in place, there’s still the possibility that your business suffers a loss from a cyberattack. Cyber insurance can cover losses your business experiences due to cyberattacks, whether they are first-party losses or losses from third-party legal claims. Commercial crime insurance can also provide protections against cyberattacks executed through social engineering fraud.
Methodology
AdvisorSmith surveyed 1,122 people who own or manage a small-to-medium business in the U.S., in conjunction with Momentive.ai. This survey was conducted in October 2021. The margin of error for this survey was less than or equal to 3%.
Forty-eight percent of respondents were male, and 52% of respondents were female. In terms of age, 27.3% of respondents were between the ages of 18-29, 40.2% were between 30-44, 18.4% were between 45-60, and 14.1% were over 60.
The industry breakdown of respondents is as follows: Advertising and Marketing (8.9%), Agriculture (5.2%); Airlines & Aerospace (2.1%); Automotive (3.6%); Business Support & Logistics (6.0%); Construction, Machinery, and Homes (6.2%); Education (9.4%); Entertainment & Leisure (5.1%); Finance & Financial Services (4.6%); Food & Beverages (4.8%); Government (2.9%); Healthcare & Pharmaceuticals (10.2%); Insurance (1.0%); Manufacturing (3.1%); Nonprofit (4.2%); Retail & Consumer Durables (9.5%); Real Estate (4.2%); Telecommunications, Technology, Internet & Electronics (5.5%); Transportation & Delivery (1.9%); and Utilities, Energy, and Extraction (1.5%).
Expert Commentary
AdvisorSmith spoke with the following experts to provide critical insight on cyber risk for small business owners.
More Experts
Q. Should small businesses be concerned about cyber risk?
Paul: Small businesses should absolutely be concerned about cyber risks. Common types of attacks, such as ransomware, could prove devastating to small or midsized organizations.
Small businesses have relatively higher reliance on their technology base, whereas a cyberattack on a large organization could be very damaging but not entirely disruptive. In contrast, a small enterprise could easily see a cyber event cascade against their relatively smaller technology architecture before they could mount an adequate response.
Additionally, small enterprises that are part of supply chains that include large enterprises are targets. Attackers understand a breach to a small member of the supply chain could give them access to the systems of larger partners (e.g. Target).
Finally, small enterprises are subject to the same legal and regulatory requirements related to privacy and data protection. Inadequate security could represent non-compliance, leaving the organization vulnerable to substantial penalties.
Darryl: Yes. A lot of small businesses do business with larger businesses, therefore, are required to take a closer look at their security awareness and preparedness.
Raymond: All businesses, regardless of size, should be concerned about cyber risk and should take steps to identify and assess them and then take proportionate action to eliminate, mitigate, or transfer them in accordance with their risk appetite. Cisco CEO John Chambers once remarked, “There are two types of companies: those who have been hacked, and those who don’t yet know they have been hacked.” Given the seemingly inevitability of cyberattacks, successful businesses tend to be those that acknowledge and respond to cyber risk. Fortunately, there are strategies and resources businesses can call upon.
One such strategy is recommended by Bruce Schneier, in his book Beyond Fear: Thinking Sensibly About Security in an Uncertain World. Bruce presents a simple and practical five-step process for evaluating the value of a countermeasure against security attacks, including cyberattacks. His approach is particularly helpful in ensuring hype does not interfere in the process. One resource every business should explore is insurance, particularly cyber insurance.
Cyber insurance can be an effective countermeasure by serving as a means of transferring cyber risk away from the business to the insurance company. This helps to mitigate losses resulting from cyber-attacks. It should therefore be considered a valuable weapon that businesses can use to address cyber risk.
Ahmed: Yes, definitely, no matter what the size of the company, you need to be worried about cyber risk. It’s similar to allowing someone to get into your house, office, or building without your permission and have no idea what they will do.
In 2020, according to FBI reporting, cyberattacks cost Americans $4.2 billion, with around $2 billion via phishing emails.
Some interesting stats:
- Only 2% of IT budget is used for security
- 70% of employees don’t understand cybersecurity
- 30% of the world’s top websites are unsecure
- Outdated and unpatched software constitutes 22% of security issues
- 68% of business don’t have cybersecurity insurance
- 68% don’t have a disaster recovery plan in place
- SMBs are targeted 43% of the time
- Small businesses invest <$500 per year in cybersecurity products
Q. How can a business effectively organize and manage cyber risk?
Paul: Enterprises must develop appropriate governance, risk, and compliance frameworks to effectively manage cyber risks. There is ample guidance, including the ISO 27000 series framework that outlines the Information Security Management System as well as the NIST Cybersecurity Framework. Adoption of standards such as ISO 27000 and NIST CSF can guide organizations to understand and treat the majority of general cyber risks, as well as establish a foundation to assess unique risks to their enterprise.
Darryl: Ransomware is running wild amongst all sizes of businesses. One of the many ways to recover from a ransomware attack is to have good offsite backups. This is in conjunction with a good business continuity plan. A good business continuity plan is not only after a disaster but one that is done before, during, and after a disaster.
In addition to ransomware, there is phishing, malware, weak passwords, web applications, and insider threats. Some mitigation to these things include good security training for employees (i.e., how to recognize a phishing attempt). The business should have these trainings several times a year.
A business should also have end-point protection, including anti-virus and anti-malware software on desktops/laptops. The business should also have good security policies, including a BYOD (Bring Your Own Device) policy, a mobile device policy, and policies around what to do if you think you got phished in addition to what websites to avoid or are prohibited.
Offsite backups are also important. The business should keep its backups separate from its main network. So if your network gets attacked, your backups are in a separate safe area. This can be in the cloud or just in a different physical location.
Raymond: The process of effectively organizing and managing cyber risk can be very challenging depending on the complexity of the business. Fortunately, many great sources offering specific guidance on organizing and managing cyber risk are available.
The Federal Trade Commission, for example, offers a variety of guides are resources at their website. Of course, media outlets often release pertinent articles (e.g., Forbes) that businesses should regularly review to help remain informed of the current cyber-threat landscape. Businesses should familiarize themselves with such resources and select those most appropriate for their particular situation and needs.
One resource, the cyber risk matrix, can be particularly helpful in organizing and managing cyber risk. A cyber risk matrix can be used to condense and visually convey cyber risks and therefore help decision makers in making sound cyber risk management investments. Businesses should also explore security education training and awareness (SETA) strategies as they often yield the greatest return on investment when addressing cyber risk. Regardless of choice of resources and action plans, businesses should commit to formulating a plan of action and then following through by implementing the plan.
If the plan includes some form of cyber insurance, extra care should be taken in learning the different forms that are available in this emerging market. Businesses should understand the differences between data breach coverage versus general cyber liability insurance. A clear understanding of the differences will help ensure the selected coverage appropriately targets the corresponding cyber risk.
Ahmed: When I teach cybersecurity class at SJSU, we always talk about three levels of protection like three circles inside each other:
- Technology Solutions: for example, installing firewalls, anti-virus, anti-spyware, patching management
- Business Policies and Procedures: for example, changing your password every 90 days, using two-factor authentication (2FA), annual training of employees on cyber risks
- Industry Standards and Laws & Regulations: for example, minimum security requirements like changing the default password, including security protocol in the design of software and hardware at early stages instead of as an afterthought, complying with the California Consumer Privacy Act (CCPA) and the General Data Protection Regulation (GDPR)
Q. Where do you see the cyber insurance market trending, and what are the main insurability challenges?
Paul: The cyber insurance industry is at a crossroads as it attempts to confront the growing payouts related to ransomware attacks. Current discussion is particularly focused on dropping coverage for ransom payments; however, the substantial costs for response and recovery have grown as well. Insurers recognize broad restrictions to payouts on ransomware costs could have a stifling effect on demand for policies but are challenging to model the exposure in this changing landscape.
Another factor to consider is the lack of reasonable means to price policies across organizations. Essential capabilities such as network security controls, anti-malware, and backup/recovery can reduce the impact of ransomware attacks. However, beyond that, there is little opportunity to differentiate risk levels between organizations, as much of the risk revolves around human behaviors such as clicking malicious links, weak passwords, etc.
In other words, insurers trying to judge relative levels of organizational preparedness against ransomware threats (as an input to pricing) find it difficult to identify relevant, observable indicators of preparedness.
Darryl: The biggest challenge is keeping up with the ever-changing world of hacking. Security IT people have a hard time keeping up with all the challenges.
I would see the insurance and cybersecurity industries working together more. Like the model for “good driving,” you get credits or something back. I could see manufacturers getting credits for showing that they have secure devices (IoT, cars, etc.).
I read somewhere that they may start having cyber insurance for individuals and families. This might backfire where the hackers will go for them instead of the businesses. It just extends the attack surface to where the hackers have another group that is insured and they know they could pay out their ransoms.
I don’t know if this exists, but the reinsurance business is big. They do this for hurricane disasters. But again, this would encourage the hackers to do more because they will get the insurance money instead of the business. They really don’t care where the money comes from.
Insurers will definitely need to revisit their underwriting practices and see different ways they can award their clients for better cybersecurity practices.
I know that IT/cybersecurity audits are needed, and maybe that is where they could form a branch to go out to businesses and run audits, like public companies do now for SOX compliance. Then give discounts for companies who have gone through one of these audits.
Raymond: The cyber insurance market is very dynamic and continues to evolve. So too, are the forms of cyber risks. More cyber insurance options are becoming available, each tailored to providing protection, through transference of risk or mitigation of losses, for different cyber risks. Ransomware attacks are currently trending due to the frailty of human nature to resist social engineering attacks and since cybercriminals now offer ransomware-as-a-service (RaaS) options. As mentioned earlier, SETA campaigns are a relatively simple and cost-effective means of preventing employees at all levels from falling victim to ransomware attacks. Failure to plan and act ensures a business remains vulnerable.
General neglect or failure to adequately address cyber risk associated with ransomware and other cyber threats seems to be driving the cyber insurance market to impose additional insurability restrictions, exclusions, and conditions. In turn, businesses wishing to obtain cyber insurance are increasingly being required to engage in practices, such as SETA, that address insurer requirements. By engaging in effective management of cyber risk, businesses can reduce their need for insurance.
As always, businesses should consult with their technology leadership, legal counsel, and insurers to fully apprize themselves of their cyber risks and management options.
Ahmed: With almost 68% of business without cybersecurity insurance, education of insurance benefits is lacking. Perception of this kind of insurance is not high on the list of businesses, and small businesses spent less than $500/year on cybersecurity. The cost of cyber insurance is a challenge, especially with many small business owners looking at cybersecurity insurance as an expense instead of an investment in protecting the business from the three outcomes of any cyberattack: litigation, reputation, and business loss. So lower cost and more info about this kind of insurance will make it possible to convince small business owners to consider it.








